10 Aug 4 Types Of Fingerprint Scanners: Deep Dive Into How They Work
What is a fingerprint scanner?
A fingerprint scanner, often referred to as a fingerprint sensor or reader, is an electronic device designed to capture and digitally analyze fingerprint patterns. The primary function of these scanners is to provide authentication and security, as fingerprints are unique to each individual, making them a reliable way to confirm a person’s identity.
Table of Contents
Types of fingerprint scanners.
There are different types of fingerprint scanners, and they work based on various principles:
Optical Scanners:
These are the oldest type of fingerprint scanners. They work using a light-sensitive microchip (either a charge-coupled device or a CMOS image sensor). When a finger is placed on the scanner, it illuminates the skin’s surface and captures an image of the fingerprint.
Capacitive Scanners:
These scanners measure the minute differences in electrical charge across the surface of the skin. When a finger is placed on the scanner, the ridges in the fingerprint touch the scanner’s surface while the valleys don’t. This creates a pattern of capacitance variations that can be translated into a digital image of the fingerprint.
Ultrasonic Scanners:
These scanners utilize ultrasound waves to detect the details of fingerprints. The scanner sends out an ultrasonic pulse which bounces back to the sensor after hitting the ridges and valleys of the fingerprint. The returning sound waves are captured and processed to form an image.
Thermal Scanners:
These are less common and work by detecting the temperature differences between the ridges and valleys of the fingerprint.
How does the optical fingerprint scanner work?
Example: MANTRA Morphs Scanner.
Example: ZKTEKO USB Fingerprint Scanner
Example: Digital Persona USB Fingerprint Sensor
Optical fingerprint scanners are one of the most common types of fingerprint readers, especially in earlier applications of the technology. They function by capturing an image of the fingerprint using light, much like how a digital camera works. Here’s a deeper look into their operation:
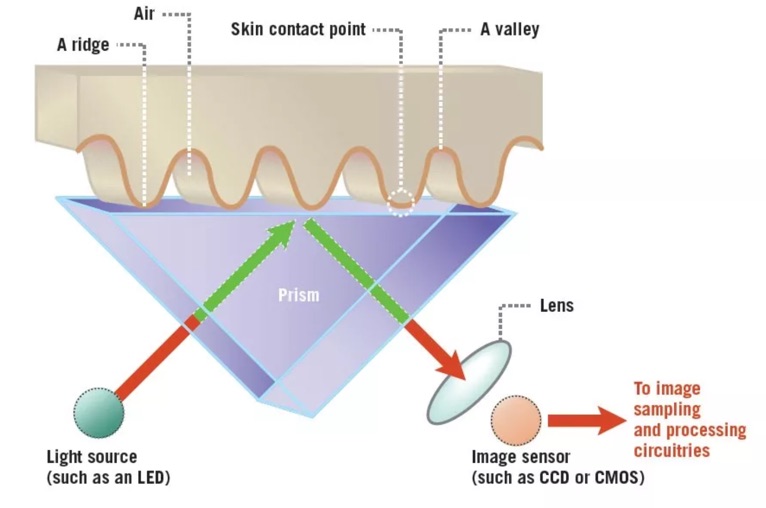
Principle of Operation:
At the core, optical fingerprint scanners rely on the fact that the ridges and valleys of a fingerprint have different reflective properties. Ridges in a fingerprint are the raised parts, while valleys are the recessed areas between ridges. When light shines on a finger, the ridges reflect it directly, while the valleys scatter it.
Image Capture:
When a finger is placed on the scanner’s surface, usually made of glass or a similar transparent material, it gets illuminated, typically by an LED light.
The light reflects off the finger and into a light-sensitive microchip (either a charge-coupled device or CCD, or a complementary metal-oxide-semiconductor or CMOS sensor).
The sensor captures the image based on the pattern of light and shadow created by the ridges and valleys of the fingerprint.
Image Processing:
The analog image captured by the sensor is converted into a digital format.
The digital image might then undergo various processing steps to enhance the clarity and contrast, remove noise, and make the fingerprint details more distinct.
The final processed image is then used for comparison against stored fingerprint templates.
Minutiae Extraction:
The primary features used for fingerprint comparison are the minutiae points, which include ridge bifurcations (where a ridge splits in two) and ridge endings (where a ridge ends). Sophisticated algorithms extract these minutiae points from the captured digital image, creating a map of their locations and directions. This map, rather than the full fingerprint image, is what’s typically stored and used for future comparisons, both to save storage space and for privacy considerations.
Comparison and Matching:
When a fingerprint is scanned, its extracted minutiae are compared with the stored templates. If there’s a sufficient match based on the algorithm’s criteria, the scan is deemed successful.
Challenges:
Optical scanners have some inherent challenges:
Spoofing:
Because they rely on capturing a 2D image, they can sometimes be fooled by a good quality photograph or a fake fingerprint.
Wear and Scratches:
The glass surface of the scanner can get scratched or dirty over time, affecting the quality of captured images.
Variability in Finger Conditions:
Wet, dry, or aged fingers can sometimes cause issues with image capture due to the variations in reflective properties.
Despite these challenges, advancements in the technology and the combination of optical scanners with other types of sensors or authentication methods have made them more reliable and secure over time.
Where are optical fingerprint scanners typically used?
Optical fingerprint scanners, due to their relatively simple construction and ease of use, have found application in a wide range of sectors and devices. Here are some typical uses of optical fingerprint scanners:
Access Control Systems:
One of the primary uses of optical fingerprint scanners is in systems designed to control access to buildings, rooms, or certain areas. This can be seen in office buildings, research facilities, and even some residential complexes where secure access is necessary.
Time and Attendance Systems:
Companies use these scanners in conjunction with time-keeping systems to ensure employees are present when they claim to be. By using fingerprints, the system can prevent fraudulent activities like “buddy punching” where one employee clocks in or out for another.
Computer and Mobile Device Authentication:
Some older models of laptops and smartphones had optical fingerprint scanners for user authentication. Although newer devices often use capacitive or ultrasonic scanners due to their smaller form factor and higher security, optical scanners were among the first to be integrated into consumer electronics.
Law Enforcement and Immigration:
Fingerprinting is a standard procedure in law enforcement for identifying individuals, and optical scanners provide a way to quickly and digitally capture these prints. Additionally, at border control points, optical fingerprint scanners might be used to verify the identity of travelers against biometric databases. Example: ADHAAR.
Banking and Financial Services:
ATMs and other transaction points might incorporate optical fingerprint scanners to authenticate users, adding an extra layer of security beyond a traditional PIN or password.
Point-of-Sale Systems:
In some regions, point-of-sale (POS) systems allow users to authenticate payments using their fingerprints. This can provide a quicker and potentially more secure method of transaction than entering a PIN or signing.
Safety Deposit Boxes:
Some banks and private vaults offer safety deposit boxes with optical fingerprint scanning systems as an added security measure.
Vehicle Access:
Some high-end or custom vehicles might use optical fingerprint scanners as a method of keyless entry or ignition, ensuring only authorized users can access and start the vehicle.
While optical fingerprint scanners are versatile and have been widely adopted, their use in certain applications, especially compact devices like modern smartphones, has decreased in favor of newer technologies like capacitive and ultrasonic scanners. These newer technologies often offer greater accuracy, resistance to spoofing, and more flexibility in design integration. Nonetheless, optical scanners remain prevalent in many applications due to their reliability and established track record.
Optical Fingerprint Scanners: Size Considerations
Optical fingerprint scanners operate by capturing a visual image of a fingerprint using light, similar to how a digital camera functions. This modality inherently requires certain components that influence the overall size and form factor of the scanner. Two primary components are the light source and the glass pane, both of which contribute to making optical scanners relatively larger in size compared to some other types of fingerprint scanners.
Light Source:
Optical scanners necessitate a light source, typically LEDs, to illuminate the fingerprint. The light reflects off the finger’s ridges and valleys, creating a pattern that can be captured and analyzed. Incorporating this light source requires additional space both for the LED components and the associated electronics.
Glass Pane:
For the scanner to capture the reflected light from a fingerprint, there needs to be a clear medium through which the light can travel. This is where the glass pane (or a similar transparent material) comes in. The user places their finger on this pane, and the light reflects off the finger, passing through the glass to be captured by the light-sensitive microchip beneath. This glass pane needs to be of a certain thickness to ensure durability, especially since users will repeatedly press their fingers against it. Its presence adds to the depth and overall size of the scanner.
Because of the intrinsic requirement for these components, optical fingerprint scanners often have a distinct, raised area or a noticeable section on devices, particularly when compared to more recent technologies like capacitive or ultrasonic scanners. While advancements in miniaturization have reduced the size of optical scanners over the years, there’s a limit to how much they can be downsized without compromising their functionality.
This size consideration is one reason why, in devices where space is at a premium (like modern smartphones), manufacturers have moved towards other scanning technologies that allow for more seamless integration, such as under-display ultrasonic or capacitive sensors. However, for applications where size isn’t the primary concern and reliability and durability are paramount, optical scanners remain a popular choice.
How do capacitive fingerprint scanners work?
Capacitive fingerprint scanners, as the name suggests, operate based on the principles of capacitance, which is the ability of an object to store electrical charge. Here’s a detailed look at how capacitive fingerprint scanners work:
Principle of Operation:
The fundamental principle behind capacitive fingerprint scanning is the difference in capacitance between the ridges and valleys of a fingerprint. The human skin, being an excellent conductor, and the air (or space) in the valleys between the ridges of the fingerprint, being an insulator, create distinct capacitance values that can be measured.
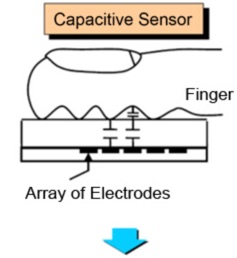
Sensor Array:
A capacitive scanner contains an array of tiny capacitor circuits. When a finger is placed over this array, each capacitor can measure the capacitance of the corresponding small portion of the fingerprint it’s aligned with.
Capacitance Differences:
When a ridge of the fingerprint comes in direct contact with one of these tiny capacitors, the capacitance changes because of the close proximity of the conductive skin.
Conversely, the valleys (spaces between ridges) don’t touch the capacitors directly. As a result, there’s a difference in the distance from the capacitor, leading to a different capacitance value due to the insulating air or space.
This differential in capacitance across the sensor array, caused by the unique pattern of ridges and valleys in each fingerprint, is what the scanner captures.
Generating an Image:
Once the capacitance values are measured across the array:
The values are converted into a digital format.
This data can be processed to produce a visual representation or image of the fingerprint or can be analyzed directly to extract unique fingerprint characteristics.
Minutiae Extraction:
As with other fingerprint scanners, the main features used for fingerprint recognition are minutiae points, which are the unique attributes of a fingerprint such as ridge endings and bifurcations. Algorithms analyze the generated data to identify these minutiae and create a map or template of their locations and directions.
Comparison and Matching:
When a fingerprint is scanned, its extracted minutiae are compared with the stored templates. If there’s a sufficient match based on the algorithm’s criteria, the scan is recognized as valid.
Advantages and Challenges:
Advantages:
Capacitive scanners are harder to spoof than optical scanners because they require the physical properties (capacitance) of a real finger. They can also be made relatively compact, making them suitable for integration into mobile devices.
Challenges:
They can be sensitive to external conditions. Dirt, oil, sweat, or moisture on the finger can alter the capacitance and potentially affect scan accuracy. Moreover, the scanners can wear out over time, especially if the surface gets scratched, reducing their effectiveness.
Modern smartphones and other electronic devices commonly use capacitive fingerprint scanners, given their compact nature and high degree of accuracy. In many cases, these scanners are integrated into buttons or specific areas of the device’s surface for easy access and use.
Where are capacitive fingerprint scanners typically used?
Capacitive fingerprint scanners have gained immense popularity due to their compact design, reliability, and resistance to common spoofing techniques. Here are some of the typical uses of capacitive fingerprint scanners:
Smartphones and Tablets:
One of the most widespread applications of capacitive fingerprint scanners is in smartphones and tablets. They provide a quick and secure method for users to unlock their devices, authenticate app purchases, and log into applications.
Laptops and Computers:
Many modern laptops and personal computers feature capacitive fingerprint readers, either integrated into a power button, touchpad, or as a standalone sensor. This offers users a secure and convenient way to log in, especially when combined with other authentication methods.
USB Security Keys:
Some USB-based security keys (often used for two-factor authentication) incorporate capacitive fingerprint scanners to provide biometric verification in addition to or in lieu of a password or PIN.
Access Control Systems:
While various types of fingerprint scanners can be used for access control, capacitive scanners offer a balance between size, reliability, and cost. They can be found in systems controlling access to buildings, rooms, or secure areas in both commercial and residential settings.
Banking and Financial Services:
Some banks and financial institutions use capacitive scanners in ATMs or specialized transaction devices, allowing users to authenticate transactions with their fingerprints.
Smart Locks and Safes:
The smart home industry has been integrating capacitive fingerprint scanners into products like door locks and safes. This provides homeowners with a keyless and pin-less access option.
Personal Electronics and Wearables:
Beyond the usual smartphones and tablets, some personal electronic devices, like certain models of earbuds or smartwatches, may incorporate capacitive scanners for user authentication.
Point-of-Sale Systems:
In certain systems, especially those designed for high-security or luxury retail environments, capacitive fingerprint scanners are used for both employee and customer authentication.
Vehicle Access and Start Systems:
Some modern or high-end vehicles feature capacitive fingerprint scanning as an option for keyless entry or ignition, ensuring only authorized users can access and operate the vehicle.
The compact nature and reliability of capacitive fingerprint scanners make them suitable for a wide range of applications. As biometric security becomes more prevalent, it’s likely that the use of these scanners will continue to expand into other areas and devices.
Capacitive Fingerprint Scanners: Popularity through Compactness and Efficiency
Capacitive fingerprint scanners have become a staple in many of our daily-use devices, especially in the realm of personal electronics. Two of the major driving forces behind their widespread adoption are their compact size and low power consumption. Here’s a note detailing these advantages:
Compact Size:
Miniaturization:
The technology behind capacitive fingerprint scanners allows for a high degree of miniaturization. The array of tiny capacitive circuits used to detect fingerprint ridges and valleys can be packed densely, making the scanner footprint small.
Integration with Devices:
The compact nature of these scanners allows manufacturers to seamlessly integrate them into a variety of devices. In smartphones, for instance, capacitive scanners have been incorporated into home buttons, side buttons, or even the back panel. Their small size ensures they don’t dominate device design, making them a preferred choice over larger optical counterparts in devices where space is at a premium.
Low Power Consumption:
Efficient Operation:
Capacitive fingerprint scanners inherently require little power to operate. They are essentially measuring changes in electrical charge, a process that doesn’t require significant energy.
Standby Modes:
Modern capacitive scanners are designed with smart standby modes. They can remain in a low-power state until touch is detected, at which point they activate and perform the scan. This power-on-demand approach ensures minimal battery drain.
Beneficial for Battery-Powered Devices:
Devices like smartphones, tablets, and wearables have limited battery capacities. Power-hungry components can be a significant detriment to overall battery life. The efficiency of capacitive fingerprint scanners means they can provide security and convenience without compromising battery longevity.
In conclusion, the small size of capacitive fingerprint scanners allows for versatile design integration, while their low power consumption ensures they don’t significantly impact the battery life of portable devices. These advantages have played a pivotal role in their adoption, especially in the world of mobile electronics, where both space and power are critical considerations.
How do they work?
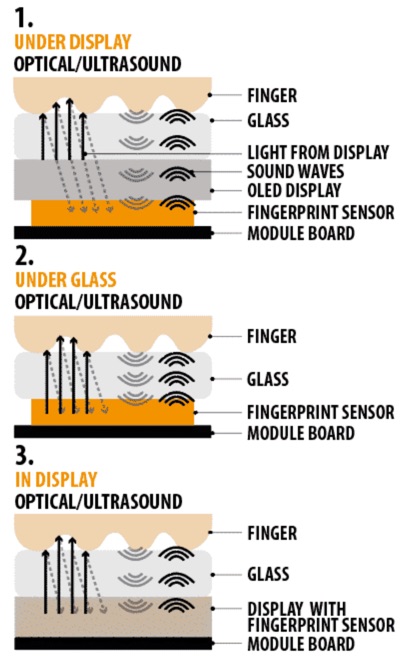
Ultrasonic fingerprint scanners represent a more recent advancement in biometric authentication. Unlike optical and capacitive scanners which rely on light or electrical differences, ultrasonic scanners utilize sound waves to detect the unique patterns of ridges and valleys in a fingerprint. Here’s a detailed explanation of how they work:
Transmission of Ultrasound Waves:
The process begins with the device transmitting an ultrasonic pulse (a very high-frequency sound wave) towards the finger that’s placed on the scanner.
Reflection and Capture:
The ridges (elevated portions) and valleys (recessed portions) of the fingerprint will reflect this ultrasonic pulse differently. The ridges of the fingerprint will come into direct contact with the scanner, reflecting the waves back immediately. In contrast, the valleys will be a bit farther from the scanner, causing a slight delay in the reflected waves.
An ultrasonic sensor (or receiver) captures these reflected waves.
Processing and Image Creation:
The data from the reflected waves is then processed by the device. Given that the reflected waves from ridges and valleys will have differences in intensity and timing, the system can construct a detailed 3D image of the fingerprint, capturing even minute details.
Advantages:
Depth Sensing:
One major advantage of ultrasonic fingerprint scanners is their ability to generate a 3D representation of the fingerprint. This depth information provides a more detailed and unique fingerprint profile, which can be harder to spoof compared to 2D representations.
Resistance to Contaminants:
Ultrasonic scanners can effectively read fingerprints even through light layers of dirt, oil, sweat, or moisture. This is because ultrasound waves can penetrate these contaminants, unlike optical or capacitive methods which can be hindered by them.
Integration Beneath Screens:
Ultrasonic sensors can be integrated beneath display panels, making them popular for modern smartphones with edge-to-edge displays. This allows for an uninterrupted screen design without a need for a dedicated button or space for the scanner.
Challenges:
Cost:
Ultrasonic fingerprint scanners tend to be more expensive than their optical and capacitive counterparts due to their complexity and newer technology.
Processing Time:
While they’re generally fast, ultrasonic scanners might sometimes be slightly slower than capacitive scanners, especially when processing the 3D image data.
In summary, ultrasonic fingerprint scanners offer a sophisticated approach to biometric authentication, leveraging the properties of sound waves to capture a detailed and unique fingerprint profile. Their ability to work through contaminants and integrate seamlessly beneath displays has made them increasingly popular, especially in high-end smartphones and devices prioritizing sleek designs and enhanced security.
Where are ultrasonic fingerprint scanners typically used?
Ultrasonic fingerprint scanners have carved a niche for themselves in the world of biometric authentication due to their unique advantages, particularly in terms of depth sensing and resistance to contaminants. Here’s where they are typically used:
Smartphones:
Perhaps the most prominent application of ultrasonic fingerprint scanners is in modern smartphones. Especially with the trend of bezel-less and full-screen designs, manufacturers have adopted ultrasonic technology to embed the scanner directly beneath the display, allowing for a seamless design without compromising on security.
Tablets:
Similar to smartphones, some high-end tablets incorporate ultrasonic fingerprint scanners to provide enhanced security while maintaining sleek design aesthetics.
Secure Access Systems:
In high-security environments, the depth-sensing capabilities of ultrasonic scanners (which make them more difficult to spoof than 2D scanners) might be favored. They can be used in secure access control systems for buildings, laboratories, data centers, and other sensitive areas.
Banking and Financial Services:
In scenarios where an extra layer of security is required, like in some ATMs or transaction devices, ultrasonic scanners can be employed.
Automotive Industry:
As vehicles become more tech-savvy, there’s a push for keyless entry and start systems. Some luxury vehicles are beginning to integrate ultrasonic fingerprint scanners as a means of authenticating the driver and granting access or starting the vehicle.
Medical Devices:
For medical equipment that requires secure access or user authentication, ultrasonic scanners can offer a reliable solution, especially in environments where the device may be exposed to contaminants, and a scanner that can operate through such obstructions is beneficial.
Personal Computers and Laptops:
While capacitive scanners are more common in this category, some high-end laptop models aiming for a cutting-edge suite of features may adopt ultrasonic scanners for user authentication.
Example: Lexar USB storage with a capacitive fingerprint sensor.
Smart Locks:
The home security industry, always evolving with technology, might see the integration of ultrasonic scanners in smart locks and security systems, especially in premium products.
Custom Applications:
Beyond these typical uses, ultrasonic fingerprint scanners might find specialized applications in various industries or custom projects where their specific advantages are deemed valuable.
As technology advances and the cost of producing ultrasonic scanners potentially decreases, we might witness an even broader application of this technology in various sectors. However, as of now, the most widespread and noticeable use remains in the realm of smartphones and personal electronics.
How do these fingerprint scanners communicate with the host?
Fingerprint scanners, irrespective of the type (optical, capacitive, or ultrasonic), require a method to communicate with the host device, be it a computer, smartphone, access control system, or any other electronic system. The primary modes of communication are typically through Universal Serial Bus (USB) and Serial Communication. Here’s a detailed note on how these scanners communicate with their host devices:
Communication of Fingerprint Scanners with the Host
1. USB Communication:
- Plug and Play: One of the main advantages of USB (Universal Serial Bus) is its plug-and-play capability. Once a fingerprint scanner is connected via USB, the host device generally recognizes it automatically, facilitating easy installation and setup.
- Data Transfer Rates: USB, especially in its later versions (e.g., USB 3.0 and USB 3.1), offers high data transfer rates. This is essential for transferring high-resolution fingerprint images or data quickly to the host device for processing.
- Power Supply: USB not only provides a data link but also supplies power to the connected device. Many fingerprint scanners are powered directly via USB, eliminating the need for an external power source.
- Universal Compatibility: Given the ubiquity of USB ports on computers, laptops, and many other devices, USB-connected fingerprint scanners can be easily used across a multitude of platforms.
- Protocols: USB communication utilizes standard protocols which ensure that the scanner and host device understand each other and can exchange data in a structured manner.
2. Serial Communication:
- Nature: Serial communication involves transmitting data one bit at a time, sequentially, over a communication channel or computer bus. It’s an older but still widely-used method of communication, especially in certain embedded systems or specific applications.
- UART (Universal Asynchronous Receiver-Transmitter): Often, devices that use serial communication will have a UART chip that facilitates this mode of communication. The UART takes bytes of data and transmits the individual bits in a sequential manner. On the receiving end, a UART will collect the bits and reconstruct the byte of data.
- Baud Rate: This refers to the speed at which data is transmitted over the serial line. It’s crucial for both the sender (fingerprint scanner) and the receiver (host device) to agree on a baud rate to ensure accurate data transfer.
- RS-232 and RS-485 Standards: These are popular standards used in serial communication. RS-232 is more common for short-distance communication, while RS-485 can handle longer distances and is used in more industrial settings.
- Flexibility: Serial communication can be used over wireless mediums, making it versatile. Some fingerprint scanners may use serial communication over Bluetooth or other wireless protocols to communicate with host devices.
- Applications: While USB might dominate in consumer electronics, serial communication is favored in specific applications like industrial systems, certain embedded systems, or scenarios where long-distance communication with the scanner is required.
In conclusion, the communication mode a fingerprint scanner employs depends on its intended application and the host device it interfaces with. Both USB and Serial Communication offer their own set of advantages, with USB being more prevalent in consumer electronics due to its ease of use, and Serial Communication being chosen for its flexibility and specific use-case advantages.
How are the fingerprint templates saved and identified by the fingerprint sensors?
Fingerprint scanners interact with host systems or devices using predefined sets of commands and responses, allowing the capture, storage, and identification of fingerprint data. Their built-in hardware components, such as Digital Signal Processors (DSPs) and microcontrollers, play a crucial role in this interaction.
Fingerprint Scanners: Command, Capture, and Communication
1. Command Reception:
- USB or Serial Communication: Whether using USB or Serial communication, fingerprint scanners receive commands from the host system. These commands are part of a protocol or command set predefined by the scanner’s manufacturer. They instruct the scanner to perform specific tasks like capturing a print, saving a template, or searching for a match.
- Command Interpretation: The scanner’s internal microcontroller interprets the received commands and takes appropriate action. For instance, when a “capture” command is received, the scanner activates its sensing mechanism to read a fingerprint.
2. Capture and Processing:
- DSP Integration: Once a print is captured, any raw data might need to be processed to enhance quality or extract features. A Digital Signal Processor (DSP) can perform these tasks efficiently and rapidly. It can handle tasks like filtering out noise, enhancing ridge patterns, or isolating minutiae points (unique fingerprint features).
- Template Creation: Post-processing, the scanner or host device might create a “template” of the fingerprint. A template is a digital representation of specific features of the fingerprint, making it easier to compare and identify without storing the full image. This conserves storage space and speeds up identification.
3. Saving and Identification:
- Storage: Many advanced fingerprint scanners come with onboard memory (often managed by the microcontroller) to store these fingerprint templates. When instructed by a “save” command, the template is stored in this memory. This onboard storage capability allows the scanner to quickly compare a new scan with stored templates without communicating with an external database.
- Matching and Identification: When a fingerprint is presented for identification, the scanner captures the print, processes it into a template, and then compares this template against its stored entries. This matching can be done using various algorithms, which might be handled by the DSP or microcontroller, depending on the scanner’s design.
4. Response and Communication:
- Feedback to Host: Once the identification process concludes, the scanner communicates the result back to the host device. This might be a simple success/failure response, or it could include additional data like a user ID associated with the matched fingerprint.
- Status LEDs or Alarms: Some scanners are equipped with visual or audible indicators. For instance, a green LED might light up for a successful match, while a red one indicates a mismatch. Similarly, beeps or alarms can provide auditory feedback.
- Security Considerations: To maintain security and privacy, most scanners don’t send back the actual fingerprint image or template unless explicitly commanded. Instead, they send back results or codes that the host system interprets.
In essence, fingerprint scanners, through their integration of DSPs, microcontrollers, and memory, have become self-contained units capable of capturing, processing, storing, and identifying fingerprint data. Their interaction with host systems, whether via USB or Serial communication, is governed by a series of commands and responses that enable seamless and secure biometric authentication.
Final Thoughts
In the realm of biometric authentication, fingerprint scanners have emerged as one of the most reliable and widespread tools, playing an integral role in various applications, from personal electronics to high-security facilities. Whether leveraging optical, capacitive, or ultrasonic technologies, these devices are meticulously designed to capture, process, and match fingerprint data with unparalleled precision.
Their integration with advanced components like Digital Signal Processors and microcontrollers ensures not only rapid processing but also the ability to interact seamlessly with host systems via established communication protocols like USB and Serial. As technology continues to evolve, and as the emphasis on security grows ever more paramount, fingerprint scanners will undoubtedly remain at the forefront, safeguarding our data, identities, and assets with an intricate blend of science, engineering, and design.